Today applications are evolving and moving to the public cloud. Amazon Web Services (AWS) offers different types of services to host these applications in the cloud. Customers are opting for hybrid cloud services because it provides the optimum architecture for application hosting and performance. This change in cloud architecture introduces a big challenge of providing a secure connection to the remote workers.
Cisco provides a comprehensive solution by offering Cisco Adaptive Security Appliance (ASAv) and Cisco Next-Generation Firewall in the AWS marketplace. These virtual appliances can integrate with the Cisco security portfolio and provides unmatched remote access VPN architecture for AWS.
Umbrella is Cisco's cloud-based Secure Internet Gateway (SIG) platform that provides you with multiple levels of defense against internet-based threats. Umbrella integrates secure web gateway, firewall, DNS-layer security, and cloud access security broker (CASB) functionality for the most effective protection against threats and enables you to extend protection from your network to branch. Cisco AnyConnect Web Security Module A guide to uninstall Cisco AnyConnect Web Security Module from your system Cisco AnyConnect Web Security Module is a software application. This page holds details on how to remove it from your PC. It is developed by Cisco Systems, Inc. Open here for more information on Cisco Systems, Inc. AnyConnect Pre-Deployment Package (Windows 10 ARM64) - includes individual MSI files Login and Service Contract Required anyconnect-win-arm64-4.10.00093-predeploy-k9.zip 08-Apr-2021. Jadyr Pavao and I have the same issue. Update: It looks like AnyConnect and the nacl-development-environment plugin may have a conflict. Following Pete's recommendation, I removed the nacl-development-environment plugin, removed and reinstalled AnyConnect, and vpn is working again.
Figure 1: Components of the Cisco Secure Remote Worker
- Cisco AnyConnect Secure Mobility Client:Cisco AnyConnect Secure Mobility Client empowers remote workers with frictionless, highly secure access to the enterprise network from any device, at any time, in any location while protecting the organization. It provides a consistent user experience across devices, both on and off-premises, without creating a headache for your IT teams. Simplify management with a single agent.
- Cisco Duo:Cisco Duo is a user-friendly, scalable way to keep business ahead of ever-changing security threats by implementing the Zero Trust security model. Multi-factor authentication from Duo protects the network by using a second source of validation, like a phone or token, to verify user identity before granting access. Cisco Duo is engineered to provide a simple, streamlined login experience for every remote user. As a cloud-based solution, it integrates easily with your existing technology and provides administrative, visibility, and monitoring.
- Cisco Umbrella Roaming Security Module: Cisco Umbrella Roaming Security module for Cisco AnyConnect provides always-on security on any network, anywhere, any time — both on and off your corporate VPN. The Roaming Security module enforces security at the DNS layer to block malware, phishing, and command and control callbacks over any port. Umbrella provides real-time visibility into all internet activity per hostname both on and off your network or VPN.
- Cisco Advanced Malware Protection (AMP) Enabler:Cisco AnyConnect AMP Enabler module is used as a medium for deploying Advanced Malware Protection (AMP) for Endpoints. It pushes the AMP for Endpoints software to a subset of endpoints from a server hosted locally within the enterprise and installs AMP services to its existing user base. This approach provides AnyConnect user base administrators with an additional security agent that detects potential malware threats happening in the network, removes those threats, and protects the enterprise from compromise. It saves bandwidth and time taken to download, requires no changes on the portal side, and can be done without authentication credentials being sent to the endpoint. AnyConnect AMP Enabler protects the user both on and off the network or VPN.
- Cisco Identity Services Engines (ISE):Cisco AnyConnect Secure Mobility Client offers a VPN posture module and an ISE posture module. Both provide the Cisco AnyConnect Secure Mobility Client with the ability to assess an endpoint’s compliance for things like antivirus, antispyware, and firewall software installed on the host. The administrator can then restrict network access until the endpoint is in compliance.
- Cisco Adaptive Security Appliance (Virtual Appliance):The Cisco Adaptive Security Appliance (ASA) is a security appliance that protects corporate networks and data centers. It provides users with highly secure access to data and network resources – anytime, anywhere. The remote users can use Cisco AnyConnect Secure Mobility Client on the endpoints to securely connect to the resources hosted in the Data Center or the Cloud.
- Cisco Next-Generation Firewall / Firepower Threat Defense (Virtual Appliance):The Cisco Firepower NGFW helps you prevent breaches, get visibility to stop threats fast, and automate operations to save time. A next-generation firewall (NGFW) is a network security device that provides capabilities beyond a traditional, stateful firewall by adding capabilities like application visibility and control, Next-Generation IPS, URL filtering, and Advanced Malware Protection (AMP).
Due to layer-2 abstraction in the cloud, it not possible to provide native firewall high availability, firewall clustering, and VPN clustering. AWS offers native services like AWS route53, AWS route tables that enable DNS based load balancing.
Traffic Flow:
- The remote access VPN user initiates a VPN connection using a hostname (example: answamivpn.com), and the DNS server returns an IP address. AWS route53 monitors all the firewalls using AWS route53 health checks
- Remote user makes the connection to the firewall
- Access the resources hosted in AWS
Recommendation for the architecture shown in figure 2:
- Each availability zone (AZ) should have multiple firewalls (ASAv or NGFWv)
- Each firewall should have a dedicated VPN pool (i.e. separate VPN pool for each firewall)
- VPN pool should be outside of VPC CIDR range, avoid overlapping networks
- Control traffic using AWS route table
- Enable weighted average load balancing on AWS route53
- AWS route53 should track firewalls public IP/elastic IP using port 443
- Cisco Duo: Multi-factor authentication
- Cisco Umbrella Roaming Security Module: DNS layer security and IP enforcement
- Cisco AMP enabler: File and Malware analysis
- Cisco ISE: Authentication and Posture
- SWC: Visibility
The architecture shown in figure 2, is a scalable and resilient design for a single VPC deployment. This architecture is based on the principle of a distributed architecture. In the case of a multiple VPN architecture, we recommend deploying bigger firewall instances (example: C5.2xl 0r C5.4xl) in a centralized VPC.
In the case of a multi-vpc architecture, we recommend deploying multiple instances of bigger firewalls in a centralized VPC (known as security-hub VPC) and the connect security-hub VPC to spoke VPCs using AWS Transit Gateway.
The AWS transit gateway can have the following types of attachments:
- VPC attachment (used for VPC and AWS Direct Connect (DX) connection)
- VPN attachment (used for IPsec connectivity to DC)
- Peering connection (used for peering two AWS transit gateway – not shown in this architecture)
Cisco Anyconnect Secure Download
Traffic Flow:
- The remote access VPN user initiates a VPN connection using a hostname (example: answamivpn.com), and the DNS server returns an IP address. AWS route53 monitors all the firewalls using AWS route53 health checks.
- Remote user makes the connection to the firewall.
- Access the resources hosted in AWS.
Cisco Anyconnect Server Free
Recommendation for the architecture shown in figure 3:
- Each availability zone (AZ) should have multiple firewalls (ASAv or NGFWv)
- Each firewall should have a dedicated VPN pool (i.e. separate VPN pool for each firewall)
- VPN pool should be outside of VPC CIDR range, avoid overlapping networks
- Control traffic using AWS route table
- Enable weighted average load balancing on AWS route53
- Use AWS Transit Gateway for interconnecting VPC
- For a hybrid cloud architecture, terminate VPN on the firewalls at the edge in the secure hub vpc or use VPN attachment on the AWS transit gateway.
- AWS route53 should track firewalls public IP/elastic IP using port 443
- Cisco Duo: Multi-factor authentication
- Cisco Umbrella Roaming Security Module: DNS layer security and IP enforcement
- Cisco AMP enabler: File and Malware analysis
- Cisco ISE: Authentication and Posture
- SWC: Visibility
Detailed information on the architecture described in figure3 is available this video: https://www.youtube.com/watch?v=ReI6I0eWyKc
Mac how to move application folder from documents to library. In addition to the above information, we recommend checking out our Cisco Secure Remote Worker design guide that addresses a specific use case of remote access VPN connection covered in the SAFE Internet Edge Architecture Guide. The design for remote access VPN connections includes the Cisco AnyConnect Secure Mobility Client, Cisco Duo, Cisco Umbrella, and Cisco Advanced Malware Protection (AMP) for Endpoints.
Design Guide: https://www.cisco.com/c/dam/en/us/solutions/collateral/enterprise/design-zone-mobility/secure-remoteDe-worker-design-guide.pdf
Thanks,
Anubhav Swami (CCIEx2: 21208)
Security Solutions Architect
Cisco Systems Inc.
Cisco Blog: https://blogs.cisco.com/author/anubhavswami
YouTube Channel: https://www.youtube.com/anubhavswami
Reference links:
Cisco SAFE design guide for AWS: https://www.cisco.com/c/dam/en/us/solutions/collateral/enterprise/design-zone-security/secure-aws-design.pdf
Cisco SAFE Cloud Architecture Guide: https://www.cisco.com/c/dam/en/us/solutions/collateral/design-zone/cisco-validated-profiles/safe-secure-cloud-architecture-guide.pdf
Cisco SAFE secure remote worker: https://www.cisco.com/c/dam/en/us/solutions/collateral/enterprise/design-zone-mobility/secure-remote-worker-design-guide.pdf
Cisco Stealthwatch Cloud: https://www.cisco.com/c/en/us/products/security/stealthwatch-cloud/index.html
Cisco AMP for Endpoints: https://www.cisco.com/c/en/us/products/security/amp-for-endpoints/index.html
Cisco Duo: https://duo.com/
Cisco Umbrella: https://umbrella.cisco.com/
Cisco ASA: https://www.cisco.com/c/en/us/products/security/asa-firepower-services/index.html
Cisco Next-Generation Firewall: https://www.cisco.com/c/en/us/products/security/firewalls/index.html
Amazon Web Service: https://aws.amazon.com/
Amazon Load Balancer: https://aws.amazon.com/elasticloadbalancing/
Amazon Route53: https://aws.amazon.com/route53/
Amazon Route Table: https://docs.aws.amazon.com/vpc/latest/userguide/VPC_Route_Tables.html
Amazon Transit Gateway: https://aws.amazon.com/transit-gateway/
Cisco Live Sessions:
NGFWv and ASAv in AWS and Azure (BRKSEC-2064): https://www.ciscolive.com/global/on-demand-library.html?search=Anubhav%20Swami#/session/1542224327848001r3qI
Deploy ASAv and NGFWv in AWS and Azure (LTRSEC-3052): https://www.ciscolive.com/global/on-demand-library.html?search=Anubhav%20Swami#/session/1564527389250001ckvR
ARM yourself using NGFWv and ASAv in Azure (BRKSEC-3093): https://www.ciscolive.com/global/on-demand-library.html?search=Anubhav%20Swami#/session/1560880389440001ntSs
YouTube Videos:
YouTube Channel: https://www.youtube.com/anubhavswami
Overview
Stanford's VPN allows you to connect to Stanford's network as if you were on campus, making access to restricted services possible. To connect to the VPN from your Windows computer you need to install the Cisco AnyConnect VPN client.
Two types of VPN are available:
- Default Stanford (split-tunnel). When using Stanford's VPN from home, we generally recommend using the Default Stanford split-tunnel VPN. This routes and encrypts all traffic going to Stanford sites and systems through the Stanford network as if you were on campus. All non-Stanford traffic proceeds to its destination directly.
- Full Traffic (non-split-tunnel). This encrypts all internet traffic from your computer but may inadvertently block you from using resources on your local network, such as a networked printer at home. If you are traveling or using wi-fi in an untrusted location like a coffee shop or hotel, you may wish to encrypt all of your internet traffic through the Full Traffic non-split-tunnel VPN to provide an additional layer of security.
You can select the type of VPN you want to use each time you connect to the Stanford Public VPN.
Install the VPN client

- Download the Cisco AnyConnect VPN for Windows installer.
- Double-click the InstallAnyConnect.exe file.
- When a message saying the Cisco AnyConnect client has been installed, click OK.
Connect to the Stanford VPN

Cloud Web Security Using AnyConnect - Cisco
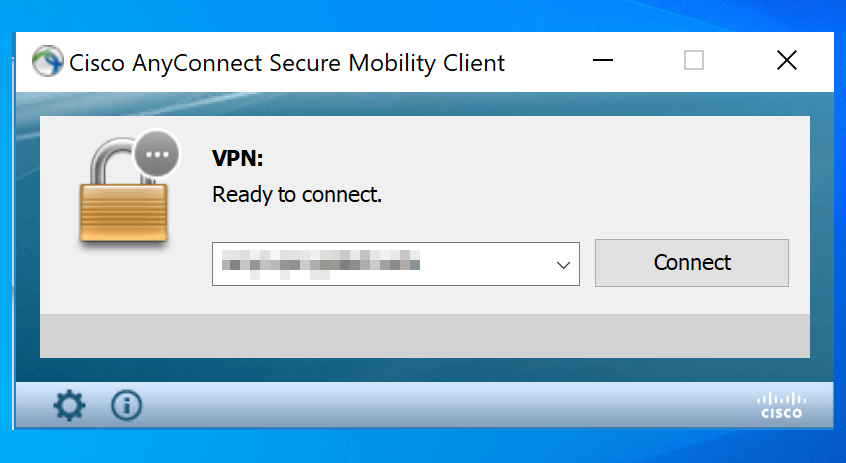
- Launch the Cisco AnyConnect Secure Mobility Client client.
If you don't see Cisco AnyConnect Secure Mobility Client in the list of programs, navigate to Cisco > Cisco AnyConnect Secure Mobility Client. - When prompted for a VPN, enter su-vpn.stanford.edu and then click Connect.
- Enter the following information and then click OK:
- Group: select Default Stanford split- tunnel (non-Stanford traffic flows normally on an unencrypted internet connection) or Full Traffic non-split-tunnel (all internet traffic flows through the VPN connection)
- Username: your SUNet ID
- Password: your SUNet ID password
- Next, the prompt for two-step authentication displays. Enter a passcode or enter the number that corresponds to another option(in this example, enter 1 to authenticate using Duo Push to an iPad). Then click Continue.
- You may have to scroll down the list to see all of your options.
- If your only registered authentication method is printed list, hardware token, or Google Authenticator, the menu does not display. Enter a passcode in the Answer field and click Continue.
- Click Accept to connect to the Stanford Public VPN service.
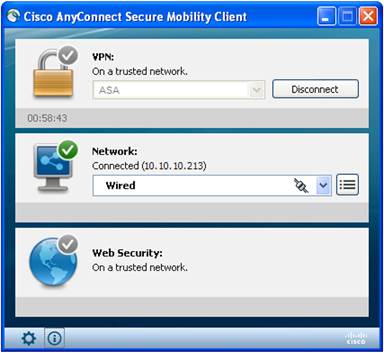
- Once the VPN connection is established, a message displays in the lower-right corner of your screen, informing you that you are now connected to the VPN.
Disconnect from the Stanford VPN
- In the notification area, click the Cisco AnyConnect icon if it is displayed. Otherwise, go to your list of programs and click Cisco AnyConnect Secure Mobility Client.
- At the prompt, click Disconnect.
